Network Security Encryption
Protecting Data as It Moves Across Your Network
Network security and encryption work together to keep data safe while it travels between devices, systems, and sites.
Good protection helps prevent attackers from reading, changing, or stealing information on company networks or over the internet
Basics of Network Security
Network security aims to protect the confidentiality, integrity, and availability of data and services.
This includes defending against threats such as malware, unauthorized access, phishing, and denial‑of‑service attacks.
Common network security tools include firewalls, intrusion detection and prevention systems, antivirus, and secure gateways.
Policies and access controls define who can connect, what they can do, and which resources they can reach.
What Is Encryption?
Encryption is a method of turning readable data (plaintext) into unreadable data (ciphertext) using a key
Only someone with the correct key can turn it back into readable form (decryption).
There are two main types of cryptography: symmetric (same key to encrypt and decrypt) and asymmetric (public and private key pairs
Modern algorithms like AES for symmetric encryption and RSA or ECC for public‑key operations are widely used to secure networks and applications.
Encryption in Network Security
1. Encryption in Transit
Encryption in transit protects data as it moves across networks, including the internet and internal links.
Protocols such as TLS/SSL secure web traffic (HTTPS), while IPsec and VPNs encrypt connections between sites or remote users and the company network.
This stops attackers from easily reading or modifying traffic, even if they can capture network packets.
It is essential for logins, financial transactions, and any sensitive communication.
2. Wi‑Fi and Wireless Security
Wireless networks must use strong encryption standards such as WPA2‑Enterprise or WPA3 to protect data over the air.
Weak or outdated methods (like WEP) can be broken quickly, exposing traffic and access credentials
Network segmentation and separate guest networks reduce the impact if a wireless segment is compromised.
Strong passwords, certificate‑based authentication, and regular updates help keep Wi‑Fi secure.
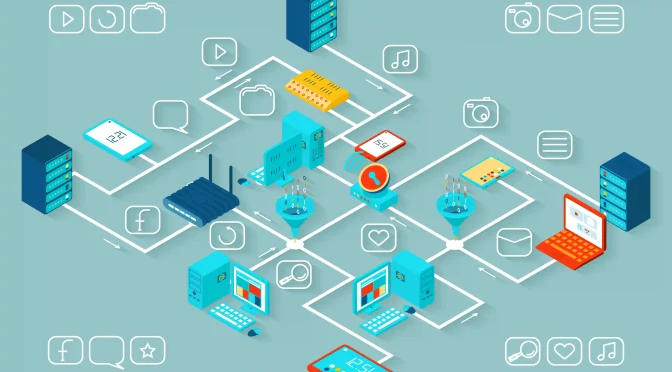
Core Technologies and Protocols
Network security uses a combination of cryptographic and security technologies:
- TLS/SSL for secure web and application traffic (HTTPS, secure email, APIs).
- IPsec for encrypting IP traffic between networks and VPN endpoints.
- VPN clients and gateways for remote workers connecting back to company resources.
- SSH for secure remote access to servers and devices.
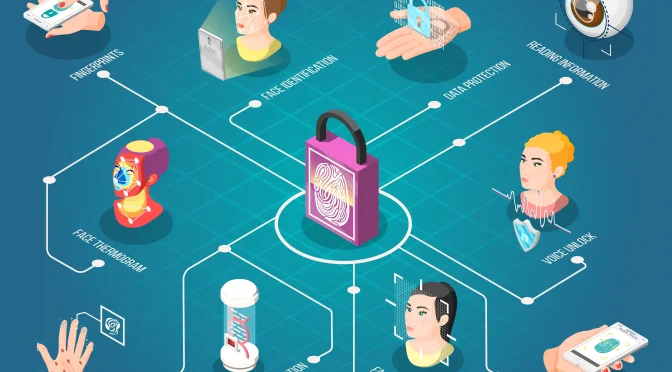
Authentication mechanisms (passwords, certificates, tokens, multi‑factor authentication) make sure that only authorized users and systems can establish these secure channels.
Best Practices for Network Security and Encryption
- Use strong, up‑to‑date encryption protocols and disable weak or legacy options
- Protect keys carefully with proper key management, rotation, and restricted access.
- Segment networks and limit access to sensitive systems with firewalls and access control lists.
- Monitor traffic and logs to detect unusual patterns, failed connections, or suspected attacks.
- Keep devices, firmware, and security tools updated to reduce known vulnerabilities.
Training employees on secure use of networks and tools is also important, because social engineering can bypass even strong technical controls.
Table: Key Areas in Network Security and Encryption
| Area | Role and main idea |
|---|---|
| Network Security Goals | Protect confidentiality, integrity, and availability. |
| Encryption Basics | Convert data to unreadable form using keys, then decrypt when needed |
| Symmetric Cryptography | Same key for encryption and decryption (e.g., AES |
| Asymmetric Cryptography | Public/private keys for secure exchange and authentication. |
| TLS/SSL (HTTPS) | Secure web and application traffic over the internet. |
| IPsec & VPN | Encrypt traffic between networks and remote users. |
| Wi‑Fi Security (WPA2/3) | Protect wireless data and access to the network. |
| Firewalls & Segmentation | Control and separate traffic between different network zones |
| Monitoring & Updates | Detect threats and keep systems patched and configured securely. |